In a world where our entire lives are stored on our smartphones, the idea of cloning a phone has become both fascinating and worrisome. But what does it really mean to clone a phone? Can we duplicate all our data, contacts, messages, and even our location? This article aims to unravel the mystery of phone cloning, exploring the possibilities, risks, and ethical considerations that come with it.
Before we dive into the details, it’s essential to recognize the privacy concerns linked to cloning a phone. Essentially, it involves making an exact copy of a device, and this brings up serious ethical and legal questions.
As we explore this topic, our goal is to provide you with a clear picture of what phone cloning entails, so you can understand its potential benefits, the risks involved, and the ethical boundaries that should guide its use.
Outline
Toggle- What Is Phone Cloning?
- How’s It Done? The Simple Breakdown:
- Methods of Phone Cloning
- 1. How to clone a phone using App
- 2. Methods to Clone a Phone Without Physical Access
- 3. Manufacturer-Provided Data Migration.
- How to Clone Phone Successfully
- Legality of Phone Cloning
- Understanding the Risk of Phone Cloning
- Signs to Identify If Your Phone is Cloned?
- FAQs
- Conclusion
What Is Phone Cloning?
Phone cloning is when you make an exact duplicate of one Android phone onto another. It sounds cool, but here’s the catch—it’s not always done for the right reasons. Some folks might try to clone a phone for stuff like unauthorized use or making calls without getting caught.
In simple terms, phone cloning is like creating a twin of your Android device, copying everything from apps to contacts. But hold on, let’s break it down step by step.
How’s It Done? The Simple Breakdown:
Now, how do people actually clone Android phones? Well, they need to get hold of some secret codes. These codes, called Electronic Serial Number (ESN) and Mobile Identification Number (MIN) pairs, are crucial for the cloning process.
Methods of Phone Cloning
It’s important to note that while there are methods for legitimate purposes like data migration, there are also illegal methods that can compromise privacy and security. Here are different methods of cloning a phone:
- App-Based Cloning
- Methods to Clone a Phone Without Physical Access
- Manufacturer-Provided Data Migration.
1. How to clone a phone using App
We’ve got a list of top-notch apps for those interested in cloning someone’s phone. These apps go beyond what your phone comes with, providing a boost in functionality. Let’s explore these user-friendly tools for an enhanced experience!
1. Using the uMOBix Tool to Clone a Phone
uMobix is an easy-to-use phone monitoring app. It’s designed for simplicity, offering features for tracking social media, including Facebook and Instagram, with updates every 5 minutes. The app goes beyond by monitoring dating apps. It also tracks the target’s real-time location and retrieves deleted messages, calls, and contacts. Additional features include surround recording, media file tracking, call management, app management, SIM card alerts, internet usage monitoring, keylogger, and device blocking.
App is Compatible with Android (version 4 and above) and iOS (with some limitations), uMobix provides ethical and reliable phone monitoring for users seeking valuable insights while respecting privacy and legality.
2. Using the Dr.Fone Clone App to Clone a Phone
Dr. Fone emerges as the optimal choice. It facilitates the seamless transfer of images, text messages, contacts, videos, and essential information, ensuring you stay in the loop with your data. Particularly beneficial during the transition from an old to a new cell phone, Dr. Fone enables the creation of an exact replica on the new device, preserving your digital history. Notably, the application boasts cross-platform compatibility, allowing effortless data sharing between Android and iOS-operating devices, enhancing its versatility and user convenience. To clone a phone using Dr.Fone, follow these simple steps:
Step 1: Install Dr.Fone on your PC or Mac.
Step 2: Connect the phone you want to copy and the target phone to your computer.
Step 3: Set one phone to send data and the other to receive.
 Once the process is complete, check the new device to ensure that all data has been successfully transferred.
Once the process is complete, check the new device to ensure that all data has been successfully transferred.
3. Using mSpy App to Clone a Phone
mSpy stands out as a top-notch mobile spy app, offering comprehensive features such as mobile phone spy software, cell phone monitoring, and GPS tracking. This app is particularly valuable for parents aiming to keep a close eye on their children’s activities. With mSpy, you can effortlessly monitor your child’s location in real-time, receiving notifications when their device enters potentially dangerous zones.
Moreover, mSpy provides robust features for managing teens’ phones. Parents can implement temporary controls, such as blocking texts during specific hours, accessing real-time call recordings, and reviewing a timeline of activities. To remotely clone someone’s phone using mSpy, follow these steps:
Step 1: Visit mSpy.com, enter your email ID, and choose your preferred plan. All plans include a 14-day money-back guarantee.
Step 2: Select the type of cell phone device you want to monitor, such as Android or iOS. Ensure you have physical access to the target phone.
 Step 3: Download the mSpy Android app on the target phone, following on-screen instructions for installation.
Step 3: Download the mSpy Android app on the target phone, following on-screen instructions for installation.
Step 4: Allow the app 2-3 hours to synchronize. Visit the mSpy dashboard online to access comprehensive information about the target phone, including texts, calls, and other details.
4. Using the ClevGuard Clone Tool
ClevGuard stands out as an advanced phone surveillance tool, offering comprehensive monitoring capabilities for those looking to clone a phone. It covers call logs, messages, call recordings, and various social media platforms such as WeChat, Viber, and Facebook.
The app excels in GPS and Wi-Fi location tracking, browsing history overview, keylogging, and previewing photos and videos—essential features when you want to clone a phone. With ClevGuard, users can capture screenshots, monitor calendar entries, and enjoy compatibility with Android, iOS, and Windows. 
2. Methods to Clone a Phone Without Physical Access
Yes, you’re not mistaken—cloning a phone without touching it is possible. We’ve simplified the process and gathered the most popular method accepted by many users.
1. Using Bluetooth
Bluetooth serves as a reliable option. This method involves two devices—the cloner’s phone and the target phone. Here are the steps in bullet points for achieving phone cloning using Bluetooth:
- Turn on Bluetooth: Activate Bluetooth on both the sending and receiving devices. and pair them.
- Select target device: Search for nearby Bluetooth devices on the sending device and choose the receiving device from the search results to establish a connection.
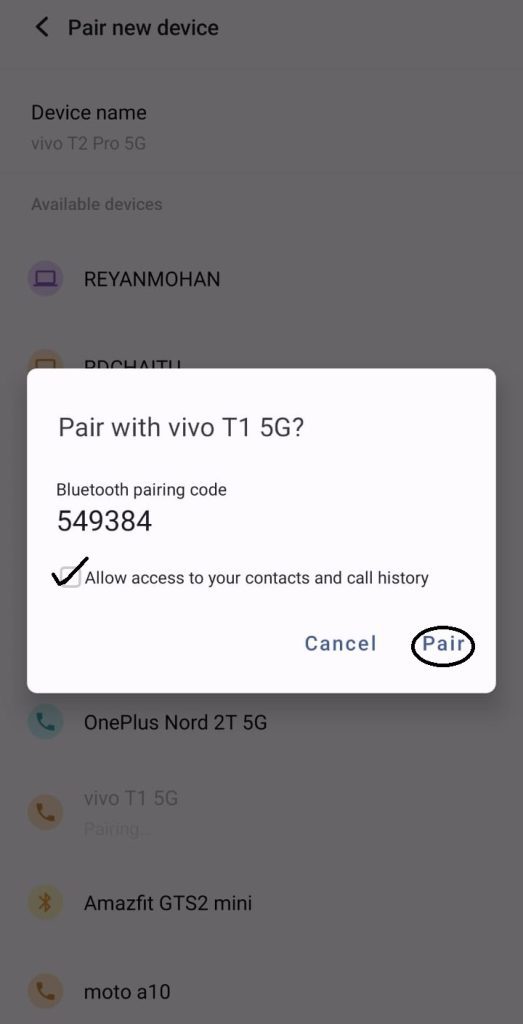
- Select data: After successful pairing, choose the files or data to be transferred on the sending device.
- Send data: Initiate the data transfer process from the sending device.
- Accept transmission: On the receiving device, confirm receipt of the transmission, usually through a pop-up window or notification.
Note: Remote cloning is not possible using Bluetooth, and the process may be slower, making it more suitable for smaller data transfers.
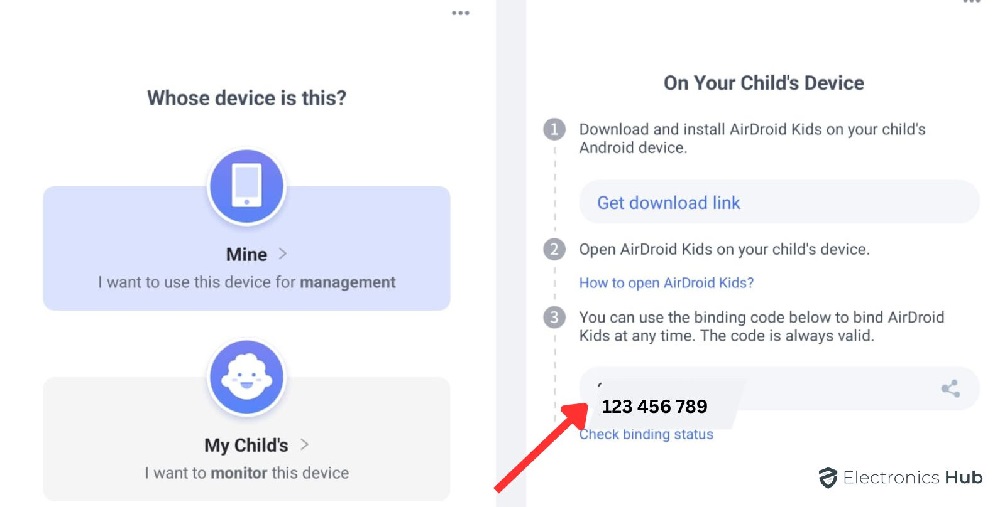
2. Using AirDroid Parental Control App
When it comes to cloning a phone without physical contact, the Airdroid Parental Control App stands out as a top choice. Designed for ensuring the safety of your children’s online activities, this app offers a range of features that make cell phone monitoring seamless.
How to Use:-
- Download app in phone available for free on Google Play Store and Apple App Store.
- create a fresh account, and log in with the same credentials on both devices.
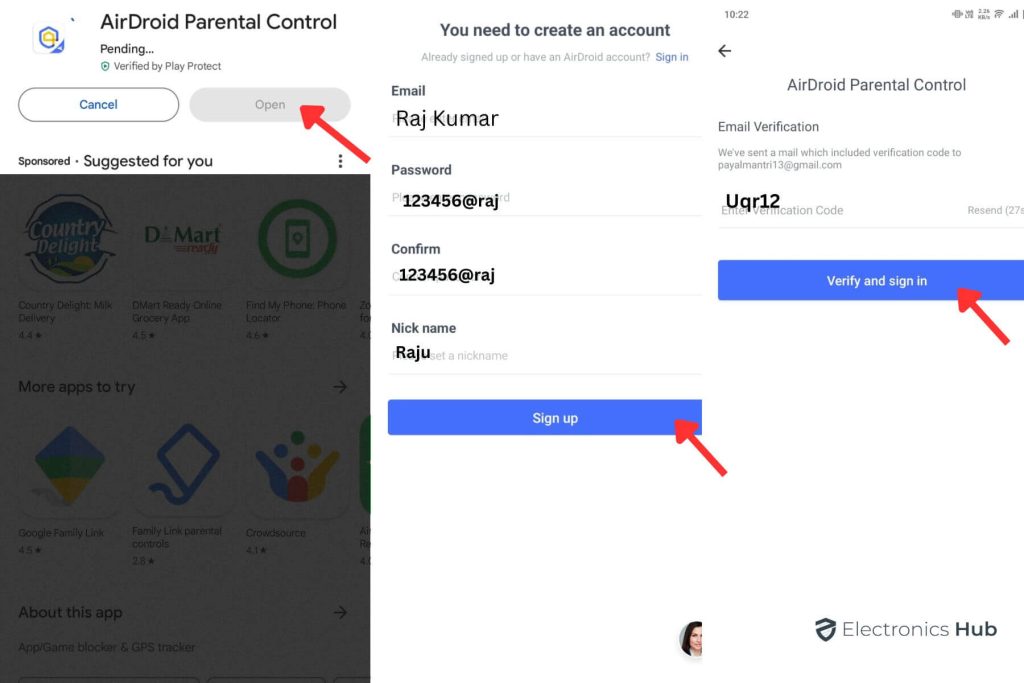
- Open AirDroid Kids on the device you want to clone.
- You will see a code which you can use to bind AirDroid Kids at any time.
3. Manufacturer-Provided Data Migration.
Manufacturer-Provided Data Migration is a feature offered by many smartphone manufacturers that allows users to seamlessly transfer their data, including apps, settings, and other content, from their old device to a new one. Certainly! Here are step-by-step instructions on how to clone a phone using Manufacturer-Provided Data Migration:
a. Prepare Both Devices:
- Ensure that both your old and new phones are adequately charged.
- Connect both devices to a stable Wi-Fi network.
b. Check Compatibility:
- Confirm that your smartphone manufacturer provides a data migration tool. Common tools include “Samsung Smart Switch” for Samsung devices and “OnePlus Switch” for OnePlus phones.
c. Access Data Migration Tool:
- On your new device, locate and open the data migration tool provided by the manufacturer. This tool may be pre-installed or available for download from the app store.
d. Choose Transfer Method:
- Select the transfer method that suits you. Options may include a wireless (Wi-Fi) transfer or using a physical connection (USB cable). Follow the on-screen instructions for your chosen method.
e. Connect Devices:
- Establish a connection between your old and new phones using the chosen method. This could involve scanning a QR code, entering a pairing code, or following other instructions provided by the tool.
f. Select Data to Transfer:
Choose the types of data you want to transfer. This may include apps, contacts, messages, photos, and settings. Some tools allow you to select specific content categories.
g. Initiate Transfer:
- Start the data transfer process. The tool will begin copying the selected data from your old phone to the new one. The duration of the transfer depends on the amount of data being moved.
h. Complete Setup on New Device:
- Follow any additional on-screen instructions to complete the setup on your new device. This may involve signing in to your accounts, setting preferences, or configuring security features.
i. Verify Data on New Device:
- Double-check that all your apps, settings, and data have been successfully cloned to your new device. Ensure that everything looks as it did on your old phone.
j. Disconnect Devices:
- Once the transfer is complete and you’ve verified that everything is in order, you can safely disconnect the devices.
How to Clone Phone Successfully
Cloning a phone successfully requires careful consideration and adherence to certain tips. Here are some key pointers for a successful cloning process:
- Research and Choose a Reliable Method: Explore and select a phone cloning method that is reputable, reliable, and suits your specific needs. Look for user reviews and expert recommendations.
- Legal Awareness: Understand the legal implications of phone cloning in your region. Ensure that you comply with all relevant laws and regulations to avoid any legal consequences.
- Backup Your Data: Before initiating the cloning process, perform a thorough backup of all your data. This step ensures that you have a copy of essential information in case of any unforeseen issues during cloning.
- Secure Connection: Maintain a stable and secure internet connection throughout the cloning process. A disrupted connection can lead to data corruption or incomplete cloning.
- Follow Step-by-Step Instructions: Carefully read and follow the step-by-step instructions provided by the chosen phone cloning method. Missing any crucial steps can result in an unsuccessful cloning or data loss.
- Verification and Monitoring: After the cloning process is complete, verify the integrity of the cloned data. Ensure that all files, settings, and applications are successfully transferred. Monitor the performance of the cloned device to identify and address any issues promptly.
Legality of Phone Cloning
Phone cloning is generally considered illegal due to multiple legal concerns. It often involves unauthorized access to personal and sensitive information, violating privacy laws. Cloning without the owner’s consent infringes on privacy rights protected by law.
Additionally, replicating unique identifiers, such as the IMEI number, raises concerns of identity theft, subject to relevant laws. Engaging in phone cloning with the intent to commit fraud or malicious activities is illegal, leading to legal consequences. Unauthorized access to accounts, messages, and personal data is covered by laws related to hacking and unauthorized access.
Understanding the Risk of Phone Cloning
Phone cloning, the process of replicating a device’s identity and data onto another device, poses significant risks to users. Here’s an in-depth exploration of the potential dangers associated with phone cloning:
- Identity Theft: Phone cloning involves copying a device’s unique identifiers, including the International Mobile Equipment Identity (IMEI) number. This opens the door to identity theft, where the cloned phone can be used for malicious activities, potentially tarnishing the victim’s identity.
- Financial Fraud: Cloned phones may be exploited for financial fraud. Attackers can gain unauthorized access to banking apps, make transactions, or leverage saved payment information on the cloned device, leading to financial losses for the victim.
- Unauthorized Access to Accounts: Phone cloning grants unauthorized access to various accounts linked to the cloned phone, such as email, social media, and messaging apps. This unauthorized access can compromise sensitive personal and professional information stored in these accounts.
- Privacy Breaches: Cloning allows unauthorized individuals to intercept calls, read messages, and access private conversations. This breach of privacy can result in leaks of confidential information or expose sensitive discussions.
- Data Manipulation and Deletion: Phone cloning provides the means for potential data manipulation or deletion. Malicious actors with access to a cloned device can alter or delete data, including contacts, messages, and files, causing significant disruptions to the user.
- Legal Consequences: Engaging in phone cloning activities is illegal in many jurisdictions. Individuals involved in cloning, whether intentional or unintentional, may face severe legal consequences, including fines and imprisonment.
- Compromised Security Measures: Cloned phones may bypass security measures set up by the original device owner, providing unauthorized access to sensitive data. This comprises the overall security of personal and professional information stored on the device.
- Device Malfunction: Improper cloning procedures can lead to device malfunctions. The cloned device may experience technical issues, disruptions in functionality, or instability, affecting the overall user experience.
- Location Tracking: Cloning enables malicious actors to track the location of the cloned device, infringing on the user’s privacy. This information can be exploited for stalking or other harmful purposes, posing a direct threat to the user’s safety.
Signs to Identify If Your Phone is Cloned?
Phone cloning is a serious concern that can compromise your privacy and security. Detecting whether your phone has been cloned requires a keen eye for unusual patterns and behaviors. Here’s a detailed guide on signs of phone cloning and steps to identify and respond to this security threat:
Signs of Phone Cloning:
- Battery Drain: Unusual battery depletion may indicate that another device is using your phone number and causing increased activity.
- Unexpected Bills: Cloning often leads to increased call or data usage. Check your phone bills for unexpected charges or abnormal usage patterns.
- Duplicated Texts and Calls: If you receive duplicate texts or calls, it could be a sign that someone is using a cloned version of your phone.
- Unexplained Data Usage: Monitor your data usage regularly. A sudden surge in data consumption without a clear reason could be a red flag.
FAQs
Ans:- Phone cloning is the process of copying the data and identity of one phone to another, essentially creating an identical replica.
Ans:- Install security apps, regularly update your phone’s software, avoid sharing personal information, and be cautious with public Wi-Fi.
Ans:- Cloning and hacking are distinct concepts in the realm of cybersecurity.
Cloning: Cloning refers to the process of creating an identical copy or replica of a device, such as a mobile phone. It involves duplicating the data, identity, and configuration settings of one device onto another. Cloning can be done legitimately, with the owner’s consent, for purposes like transferring data between old and new devices.
Hacking: Hacking is the unauthorized access, manipulation, or compromise of a device, system, or network. It involves exploiting vulnerabilities or weaknesses in security to gain unauthorized access. Hacking is illegal and occurs without the knowledge or consent of the device owner.
Ans:- No, it’s not possible to clone a phone solely with the IMEI (International Mobile Equipment Identity) number. The IMEI number is a unique identifier assigned to each mobile device, but it does not contain the necessary information or capabilities to clone a phone.
Conclusion
Phone cloning is a complex practice with ethical and legal concerns. Legitimate methods like manufacturer-provided data migration exist for legal data transfer, but unauthorized cloning is illegal and risky. Users must prioritize privacy and be cautious.
For cloning without physical access, methods like Bluetooth and apps (uMobix, Dr.Fone, mSpy, ClevGuard) exist. Use responsibly and with consent.

